Compliance failures don’t happen at a specific point in time. Small issues your team initially neglects like outdated policies, untracked third party tools, poorly configured system administration settings, lack of training, and more – all keep piling up and crashing down all at once before an audit review.
For giants like Amazon or Facebook, hefty compliance penalties are a small scratch on their reputation or revenue. Small to medium sized orgs can’t afford to compromise either, so they must take precautions to avoid common compliance mistakes.
1. Not knowing where the gap lies
This might sound cliched, but it happens more often than you’d imagine.
A fundamental mistake business leaders make is not staying updated with their legal obligations. Take this survey for example, where a shocking 37% respondents didn’t know if their org has to comply with GDPR.
Generally speaking, depending on the type of product or service, regulatory frameworks are specific. Knowing your legal obligations is critical to implementing the right controls and policies.
Once the right regulations are configured and implemented, we come to the second compliance mistake; working on the assumption that your job is done once you have passed the audit.
Regulations are continuously changing or updated with new clauses. This means staying informed about newly rolled requirements and working on non compliant areas to avoid fines or audit failures.
2. Policies can be a pickle
Policy documentation, updation, and training are de-prioritized way too often. Accountability ends up scattered across departments; requirements get reduced to checkboxes, and training gets delayed to a point of becoming an audit red flag.
Poor policy management opens gaps that regulators are ready to exploit and confusion during audit season. Avoid these common compliance policy mistakes:
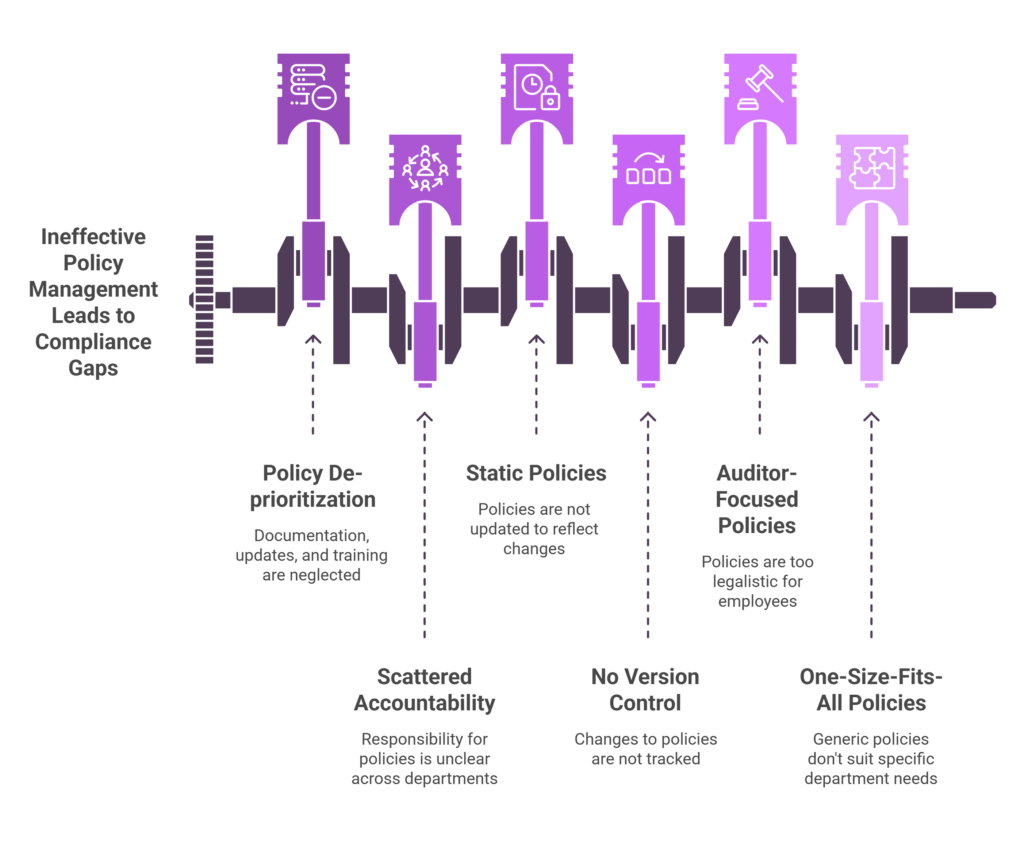
Static policies
Much like compliance controls, drafting policies is not a one and done activity, especially in a dynamic environment. New regulations, expanding into new geographies, internal structural changes, and risk assessments indicate a due policy updation.
No version control
Updating policies is step 1; step 2 is version control. Unless you don’t track what changed, when it was updated, and who approved it, you are looking at possible delays in compliance certifications.
Written for auditors, not operators
Businesses hurrying to get certified for the sake of it end up creating legal language heavy policies that are hard for employees to follow. On paper, it reflects a high compliance standard. In practice, you increase sales cycles due to increased back and forth with clients.
One size fits all policies
Fast scaling organisations rapidly adding new resources and tools cannot afford to develop generic policies used across departments. For example, marketing uses tracking tools differently than engineering handles production data. This practice inadvertently creates shadow processes, increasing violation risk.
3. Not collecting sufficient evidence
External audit investigations are rigorous, leaving no room for error. Regulatory checks can become a costly compliance mistake. More often than not, the cause of poorly collected evidence can be traced back to these:
The wrong approach
A costly error IT teams make is treating evidence collection output of the audit process, rather than a byproduct of daily operations.
For example, controls are executed in tools like IAM or ticketing systems without capturing evidence at the source. This, combined with the lack of a structured, standardized process defining what qualifies as good evidence across controls.
Over time, this approach leads to last minute audit chaos – restructuring timelines, validating activities, and bandwidth lost to chasing logs.
Collecting incomplete data
Businesses are still collecting incomplete, inaccurate, fragmented, and often incorrect data.
For example, capturing screenshots right before audits instead of doing it as a continuous activity creates a false snapshot of compliance. Last minute snapshots are easy to stage; these don’t show who performed an action – and when. These logs likely exist in the system, but unless retained and centralized, retrieval becomes challenging.
Here’s what you can do to build a mature evidence system:
- Automatically and continuously log and timestamp evidence after correctly linking it to specific users and reviewers.
- Set up a standardized process for evidence expectations for each control; where it was generated, retention period, owner, and prove.
- Centralize evidence repositories with traceable activity history. It should be version controlled and mapped directly to controls and regulatory clauses.
4. Siloed ownership, manual processes
A critical yet common cause that breaks down compliance is how you approach it. For teams implementing a single framework, using spreadsheets, emails, and basic tools might feel manageable. In theory, this works.
However, as your company scales, additional data, geographical expansion, and the broadening scope of your service might necessitate more legal obligations. This is where complications start.
Implementing multiple frameworks manually is time consuming, bandwidth demanding, and error prone. IT teams end up spending time on these activities, delaying product launch or other critical activities. Sales teams lose prospects to competitors or increase the sales cycle as customers are unlikely to proceed unless you demonstrate the ability to handle their data securely.
Manual processes, combined with siloed systems, fragmented systems further add to the chaos. Given that compliance activities require input from multiple teams, departments with little or limited visibility are prone to miscommunications and inefficiencies. Over time, this spirals into compliance violations, impacting your bottom line and credibility.
How mature organizations solve this
To minimize compliance failures, move from siloed, manual ownership to federated accountability with centralized visibility. Ensure that controls are technically actionable and align with business objectives by assigning owners.
Typically, mature compliance programs embed controls into existing workflows rather than treating them as a sales enabler or corrective measure after a breach.
Compliance activities like control monitoring, evidence collection, risk assessment, and other repetitive activities are automated. For example, GRC tools like Cura unifies fragmented compliance processes into a single system that allows teams to manage framework requirements with minimal manual effort.
5. Sales strategy and product development don’t align with compliance
Adopting compliance as an afterthought rather than a security practice is a potential cost center.
In the long run, this causes friction in product adoption and deal closure. When product teams prioritize usability and sales teams on closing deals, it opens parallel gaps.
How it disrupts product development
Product teams who develop without compliance consideration often miss foundational requirements that are difficult to incorporate later.
For example, data collection lacks a clear purpose, access controls are embedded at granular levels, and lacks mechanisms for data deletion or consent. These technical oversights create compliance gaps that are difficult to patch later for legal obligations like GDPR.
Down the line, expect revenue loss due to re-architecture cycles, delayed feature release, additional development bandwidth, and divergence from critical growth initiatives.
How it impacts sales teams
Sales teams are often under-equipped to handle compliance conversations. Customers expect clarity on data privacy measures, access controls, and accurate responses to security questionnaires.
When sales teams feel under equipped to handle high level scrutiny, compliance teams are pulled in late to compromise and the deal cycle slows down due to overpromised capabilities. Ultimately, the higher cost of delivery impacts your bottom line.
A quick guide to avoid compliance as a downstream function
Mature product teams embed compliance in system architecture like data flows, access models, and logging. Control definition and evidence generation happens at feature level instead of infrastructure.
In sales strategy, this means translating compliance posture into clear customer facing narratives. Product features are built keeping common security questions. Most importantly, features and capabilities promised by sales are actually supported in the product.
6. Third parties, compliance controls are running unmonitored
A costly mistake that breaks compliance is the assumption that one time diligence checks and control implementation is sufficient. In practice, third party risks and vendor controls drift over time, leaving security gaps.
Post the questionnaire and risk assessment checkpoint, vendor security posture changes with new data and integrations. Post approval, teams tend to lose clarity in accountability. Security assumes legal owns it; legal assumes IT tracks it.
To avoid potential breaches, set up a vendor lifecycle management system that entails real time tracking, periodic reassessments, and monitoring for changes that may be a potential risk.
Constant changes like new hires, new SaaS tools, new data flows can degrade controls no matter how well designed. Employees accumulate excessive permissions over time, shadow IT introduces unapproved tools, and data flows beyond approved boundaries.
Once you have your controls up and running, continuously monitor and test it for reviews, logging, encryption, and backup validation.
A centralized dashboard like CURA shows a single view of vendor access levels, control status, and flags high risk items.
Closing the compliance gap with a smart approach to GRC
Cura’s GRC platform helps businesses avoid compliance errors by embedding compliance into daily operations rather than treating it as a periodic exercise.
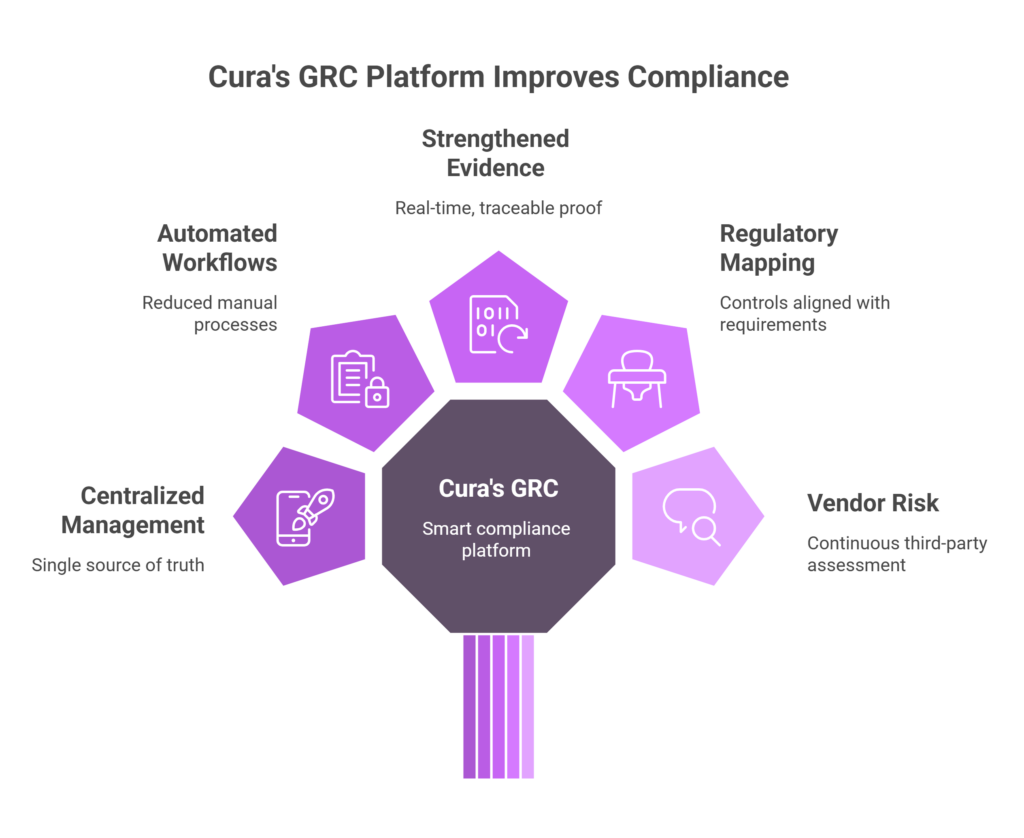
- Centralize risk, control, and policy management, eliminating fragmented systems and ensuring a single source of truth.
- Automate workflows and continuous control monitoring reduce reliance on manual processes to detect gaps before they become audit issues.
- Strengthen evidence collection and audit readiness by capturing real-time, traceable proof of control execution to remove last-minute scrambling.
- Built-in regulatory mapping keeps controls aligned with evolving requirements, while vendor risk management ensures third-party exposure is continuously assessed.
- Integrates compliance with operational systems to offer real-time visibility, proactively manage risk, accelerate audits, and move faster in enterprise sales cycles.
Don’t let compliance complications slow you down. Navigate legal hurdles and manage risk with our experts. Book a live demo now.





Leave a Reply